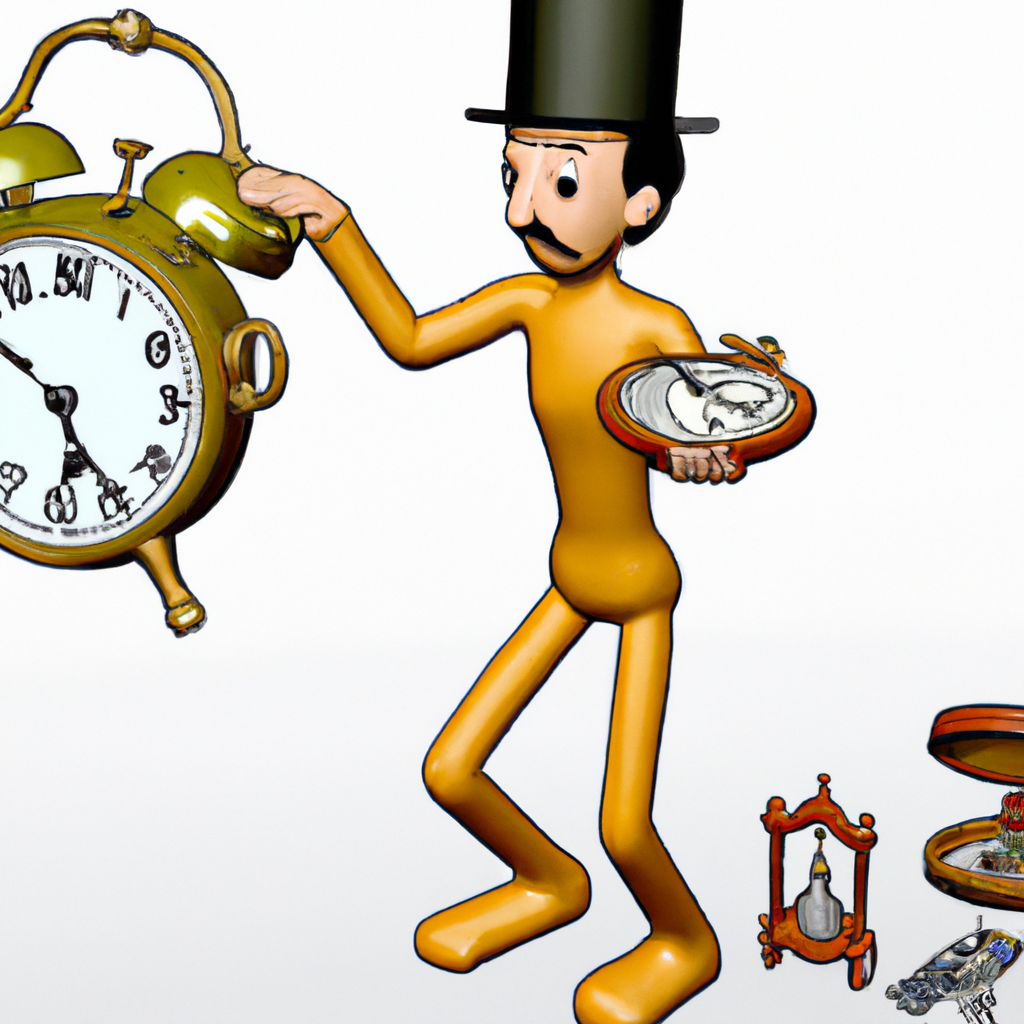
- The Target: A Collection of Rare Timepieces
- The Heist: How the Thieves Pulled it Off
- The Aftermath: The Investigation and Recovery Efforts
- The Lessons Learned: How to Protect Your Valuable Assets
The Target: A Collection of Rare Timepieces
The collection of rare timepieces that were stolen in this daring heist was worth millions of dollars. The timepieces were housed in a high-security vault in a luxury watch store in the heart of the city. The collection included some of the most sought-after watches in the world, including limited edition pieces from top luxury brands.
The thieves had clearly done their research and knew exactly what they were after. They had cased the store for weeks, studying the security measures and the movements of the staff. They knew the layout of the store and the location of the vault. They also knew the value of the watches they were after and the potential profits they could make by selling them on the black market.
The Heist: How the Thieves Pulled it Off
The heist was meticulously planned and executed by a team of highly skilled thieves. They entered the store after hours, using sophisticated tools to bypass the security system and gain access to the vault. Once inside, they quickly disabled the alarm system and began to remove the watches from their display cases.
The thieves were in and out of the store in less than 30 minutes, leaving no trace of their presence behind. They had carefully planned their escape route and had a getaway car waiting for them outside the store. The entire operation was carried out with military precision, leaving the police and the store owners stunned.
The heist was a wake-up call for the luxury watch industry, highlighting the need for better security measures and more advanced technology to protect valuable assets. It also raised questions about the effectiveness of traditional security measures and the need for more innovative solutions to combat sophisticated criminals.
The Aftermath: The Investigation and Recovery Efforts
The heist of the rare timepieces sent shockwaves through the luxury watch industry and the law enforcement agencies. The police launched a massive investigation, using all available resources to track down the thieves and recover the stolen watches. They analyzed CCTV footage, interviewed witnesses, and followed up on leads to identify the culprits.
The investigation led to the arrest of several suspects, who were found to be part of a larger criminal network involved in high-value thefts. The police were able to recover some of the stolen watches, but many of them had already been sold on the black market or smuggled out of the country.
The recovery efforts were hampered by the fact that many of the watches were unique and easily identifiable, making it difficult for the thieves to sell them without arousing suspicion. The luxury watch industry also stepped up its efforts to recover the stolen watches, offering rewards for information leading to their recovery and working closely with law enforcement agencies to combat organized crime.
The Lessons Learned: How to Protect Your Valuable Assets
The heist of the rare timepieces serves as a reminder that no matter how sophisticated your security measures are, determined criminals can still find a way to bypass them. However, there are steps that businesses and individuals can take to protect their valuable assets.
One of the most effective ways to protect your valuable assets is to invest in advanced security technology. This includes CCTV cameras, motion sensors, and alarm systems that are linked to a central monitoring station. It is also important to have a robust access control system that restricts access to sensitive areas and tracks the movements of employees and visitors.
Another important step is to conduct regular security audits to identify vulnerabilities and weaknesses in your security system. This can help you to take proactive measures to address these issues before they are exploited by criminals. It is also important to train your employees on security best practices and to have a clear protocol in place for responding to security incidents. By taking these steps, you can minimize the risk of theft and protect your valuable assets.


0 Comments